Qualys TotalCloud 2.23.0 Release Updates
Table of Contents
The Qualys TotalCloud™ 2.23.0 version introduces new capabilities, features, and updates. The release is expected to be available by mid-April 2026.
CWPP Enhancements
GCP Internal Scan
Qualys TotalCloud and Qualys VMDR now support internal network scanning for GCP Cloud Virtual Machines, using the Qualys Virtual Scanner Appliance deployed directly within your VPC. Unlike legacy IP-based scans that struggle with ever-changing address patterns, this approach targets GCP instances by instance ID, ensuring the right workloads are consistently identified and scanned, regardless of how their private IPs change over time.
This brings deep, localized vulnerability management to the parts of your cloud environment that matter most. Security teams gain accurate, inside-the-network visibility into GCP workloads without exposing them to external scan traffic, ensuring that internal exposures and misconfigurations are surfaced before they can be exploited.
CSPM Enhancements
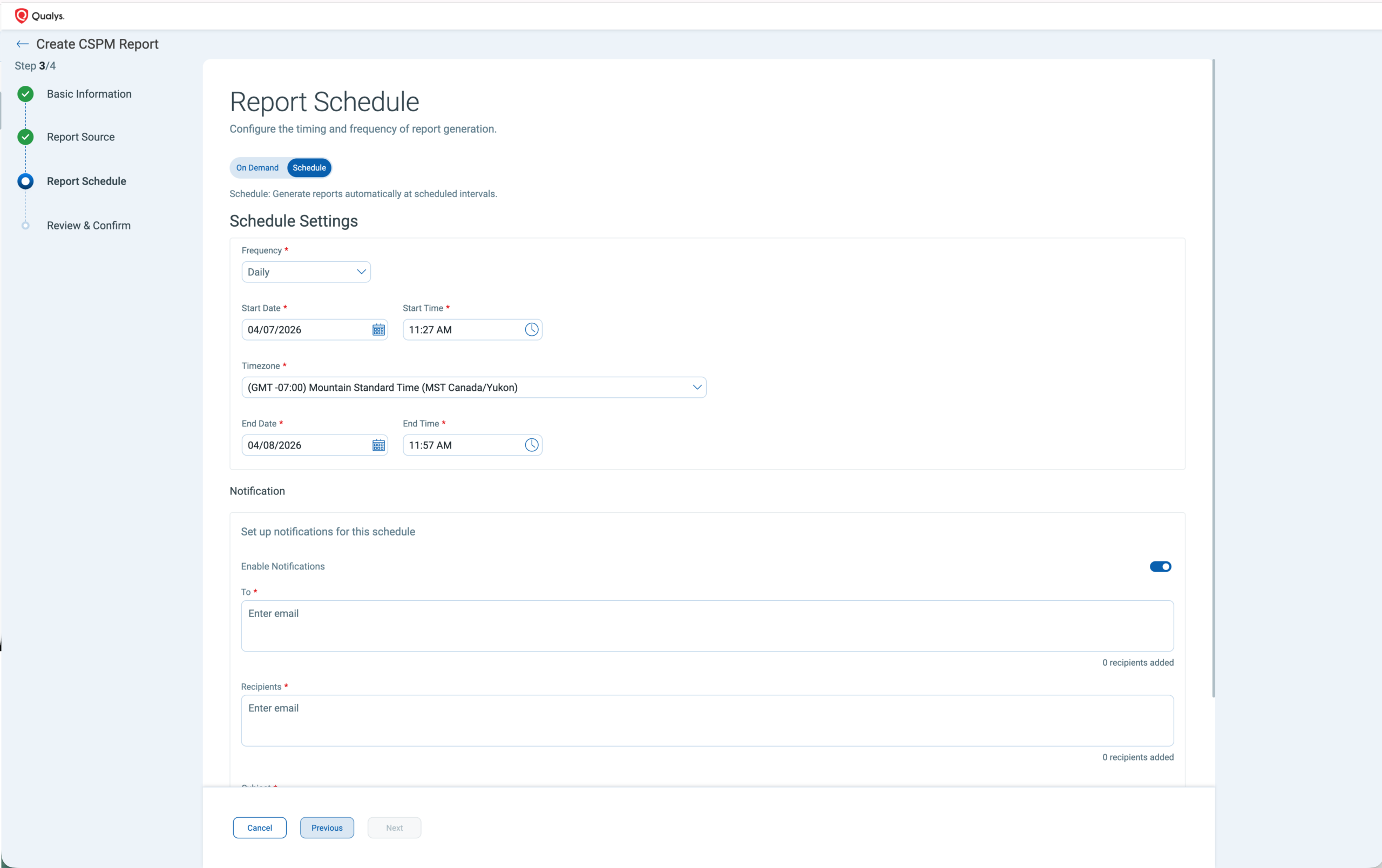
Schedule Reports and Notification
TotalCloud has extended CSPM Reporting to include scheduling and notification functionality. Security teams can configure automated, periodic reports daily, weekly, monthly, or create custom schedules scoped precisely to their cloud accounts and environments, delivered directly to custom recipient lists without any manual intervention.
By offering timely compliance snapshots, every stakeholder gets the right information at the right cadence.
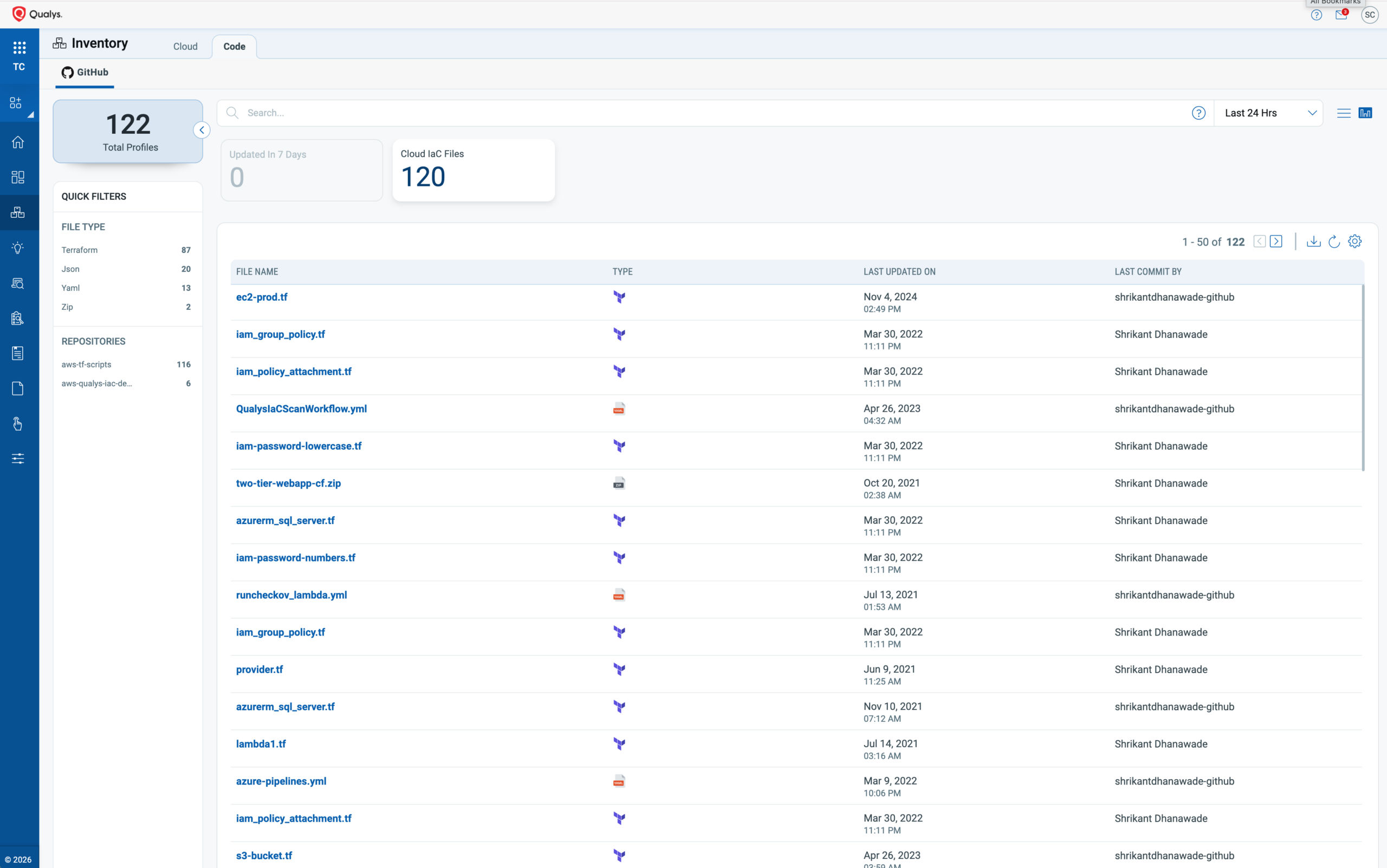
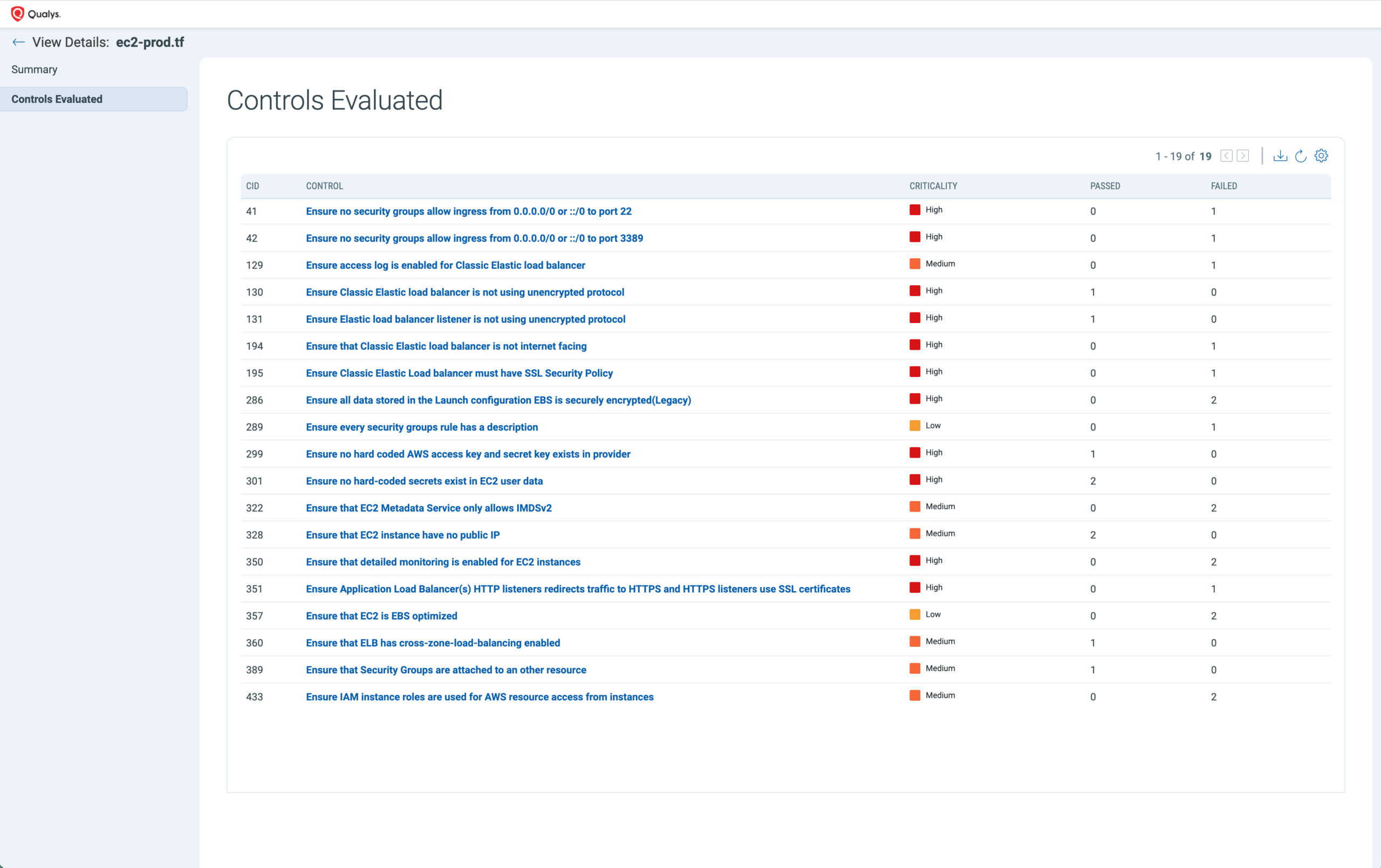
Inventory of IaC Code with co-related misconfigurations
Misconfigurations don’t just originate in the cloud; they also originate in code. TotalCloud now collects the IaC code inventory from GitHub repositories and correlates it with IaC misconfigurations detected via your existing scan integrations. We now show you cloud inventory (right side) and code inventory (left side) in the same place.
Updates to CIS Version
We have updated our CSPM policy library for the CIS Foundations Benchmarks to ensure your compliance assessments align with the latest industry standards and security best practices.
The updated support now includes:
- CIS Amazon Web Services Foundations Benchmark v6.0.0
- CIS Microsoft Azure Foundation Benchmark v5.0.0
- CIS Google Cloud Platform Foundation Benchmark v4.0.0
Key Benefits:
- Latest Security Standards: Incorporates updated recommendations to address evolving threats and compliance requirements.
- Improved Accuracy & Coverage: Reflects recent cloud provider changes for more precise risk assessments and fewer false positives.
Detection of Deleted Resources
Security teams need to know not just what exists in their cloud environment, but what no longer does. TotalCloud now tracks and displays deleted cloud resources alongside active ones, giving teams a complete lifecycle view — when a resource existed, when it was removed, and what risks it carried while it was live. This eliminates false-positive alerts on stale assets and keeps your inventory grounded in reality.
To support faster investigation, two new QQL tokens are now available across the inventory and posture tabs:
| Token | What it does |
| Not discovered (Last 7 days) | Filters resources that haven’t been seen in the last 7 days, helping surface assets that may have gone dark |
| Deleted resources | Filters confirmed deleted resources, with a clear notation on both inventory and posture tabs for quick identification |
Inventory Expansion
TotalCloud now extends its inventory coverage across cloud, network, and AI resources — giving security teams a more complete and accurate foundation for posture assessment and risk analysis.
| Inventory | What Changed | Key Benefits |
| GCP Load Balancer | We have revamped the GCP Load Balancer resource listing to surface the right resources precisely, including Load Balancing Forwarding Rules. Beyond improved inventory visibility, this enhancement directly strengthens attack path analysis, ensuring that network-level resources are accurately factored into the identification and evaluation of potential attack routes. | Complete network resource visibility, including Forwarding Rules More reliable attack path analysis with no gaps in network coverage Cleaner inventory with no phantom or missing entries |
| Increased coverage for AI Inventory | As enterprises rapidly adopt AI services, the infrastructure powering those workloads, agents, models, and pipelines is becoming a significant and often ungoverned part of the cloud attack surface. TotalCloud now extends inventory coverage to include AWS Bedrock Agents and Azure AI Foundry Agents, bringing AI resources under the same unified visibility and security assessment framework as the rest of your cloud environment. | Broader coverage of AI agents across AWS and Azure No blind spots as AI adoption outpaces traditional governance Consistent security posture across all cloud resource types |
| Removed Bedrock Foundational Models – AWS Managed Models | A precise inventory is only valuable when it reflects resources that your team owns and controls. AWS Bedrock Foundational Models are fully managed by AWS; their presence in TotalCloud’s inventory was introducing noise, inflating resource counts. By removing these AWS-managed models from the inventory, TotalCloud delivers a cleaner, more accurate view of your cloud estate, ensuring that every resource surfaced is one your team is accountable for, and that reporting reflects a true picture of your security posture without distortion. | Accurate resource counts reflecting only what your team owns Cleaner posture reporting with no AWS-managed noise Faster, more focused security reviews |
| Smarter Azure VM Discovery – Excluding Managed Service-Generated VMs from Scans | When Azure managed services like Databricks spin up background VMs to power their compute workloads, those VMs surface in your cloud inventory, consuming valuable scan licenses and inflating costs without adding security value. TotalCloud now intelligently identifies these managed service-generated VMs using key fingerprinting fields such as “Source Image Publisher” and “Source Image Offer,” and excludes them from VM scans by default. This means more accurate posture metrics and leaner operational costs, without any manual filtering overhead. | Scan licenses used only on VMs your team manages Posture metrics that reflect real security coverage Lower operational costs with zero manual overhead |
CSPM Control Enhancements
New Controls and Title Updates
We continuously monitor new security controls across cloud platforms. In this release, we have added approximately 11 new security controls for AWS IaC checks, 15 for Azure runtime checks, and several for GCP and OCI. We have also refreshed the control titles for a few AWS and OCI controls to align with the latest security checks.
For ongoing updates on these control changes, refer to the TotalCloud Release Notes for version 2.23, which will be published soon on the Qualys Product Release Notes page.
Deprecated Controls
When cloud providers deprecate specific services or features, the corresponding Qualys CSPM controls are also deprecated to maintain alignment. This ensures your compliance posture accurately reflects the current state of your cloud environments, eliminating outdated or irrelevant findings.
For more information on impacted controls, refer to the control metadata for: AWS | Azure | GCP | OCI
| Cloud Platform | Deprecated Controls | Reason for Deprecation |
| AWS | 602 – Ensure Amazon OpenSearch Service domains should have fine-grained access control enabled | Similar checks are available in other control CID 495 |
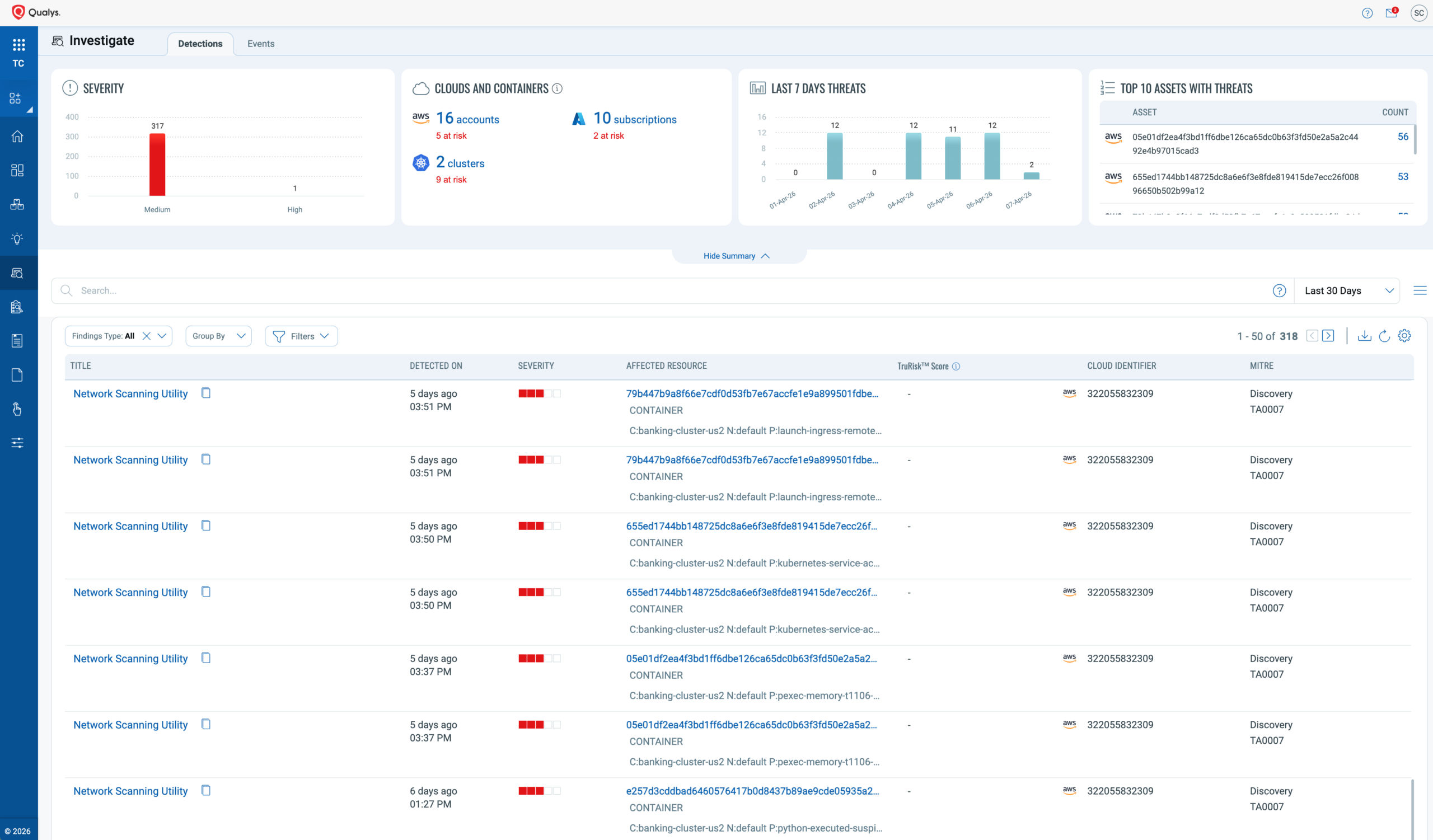
CDR Enhancements
Group by QLP in CDR Investigate
The Investigate details now support grouping detections by Qualys Locator Path (QLP), giving security teams a faster, more structured way to triage threats across their cloud environment. Qualys Locator Path (QLP) is a hierarchical, intuitive grouping framework that organizes Kubernetes containers based on their logical placement within the environment. Rather than sifting through a flat list of detections, teams can now organize findings by Cluster QLP or Container QLP, surfacing patterns and risk concentrations at a glance.
This release extends QLP grouping to container-native security contexts. CDR now supports QLP grouping dimensions, meaning detections can be traced and clustered across the full container hierarchy, from the cluster level down to the individual pod and container. Teams investigating active threats can immediately understand which part of the container stack is affected, reducing triage time and making remediation more targeted.
Hide Excepted Events
When reviewing events captured by the CDR appliance or Network Flow Logs, you can leverage exceptions to hide specific events that are known, expected, or non-actionable, reducing noise without permanently deleting any data.
CDR now lets you suppress unwanted or irrelevant events in the Investigate UI, keeping your security view focused on what matters most. This ensures your team can prioritize genuine threats while maintaining a complete and auditable record of all activity.
MITRE Mapping for All Events
TotalCloud CDR now extends MITRE ATT&CK mapping across all captured events, whether sourced from the Threat Scanner, Network Flow Logs, or the eBPF runtime. Every event is now enriched with the corresponding MITRE techniques and tactics, giving your security team a standardized, framework-aligned view of threats.
This makes it easier to understand attacker behavior, correlate events across sources, and prioritize response efforts with greater confidence.
What’s Next
- Learn more about TotalCloud™ CNAPP, the Risk-minded CNAPP
- Click here to get online help on TotalCloud, Connectors, and the TotalCloud API User Guide
- Check out the How-to Training Videos
If you have any questions, please contact your Technical Account Manager (TAM) or Qualys Technical Support.