December 2020 Releases: New RTI for Ransomware, New Password Generation Workflow, and More
The Qualys Cloud Platform December 2020 releases include Qualys Cloud Suite 10.6.0 and 3.4.0, which contain new features and important enhancements in VMDR, Policy Compliance, Cloud Agent and Dashboards.
Feature Highlights
Qualys Cloud Platform
New Workflow to Generate Password
With this release, Qualys has introduced a new workflow to generate passwords for new and existing users. Users will now receive an email containing activation URL, OTP code, and OTP key. When users click the activation URL, they need to provide the OTP code corresponding to the OTP key to view login information, including their username and password. While entering the OTP code, users must ensure that the code corresponds to the OTP Key. OTP code is valid for 30 minutes and it expires after 3 unsuccessful attempts.
This new workflow helps overcome the constraints caused by network security protocols. A Manager can change the password for any user in the subscription. A Unit Manager can do this for users in their business unit.
VMDR
New RTI and QQL for Ransomware
With this release, users can configure a ruleset to get alerts on active security threats using the new Real-Time Threat Indicator for ransomware, helping users to prioritize and take quick decisions.
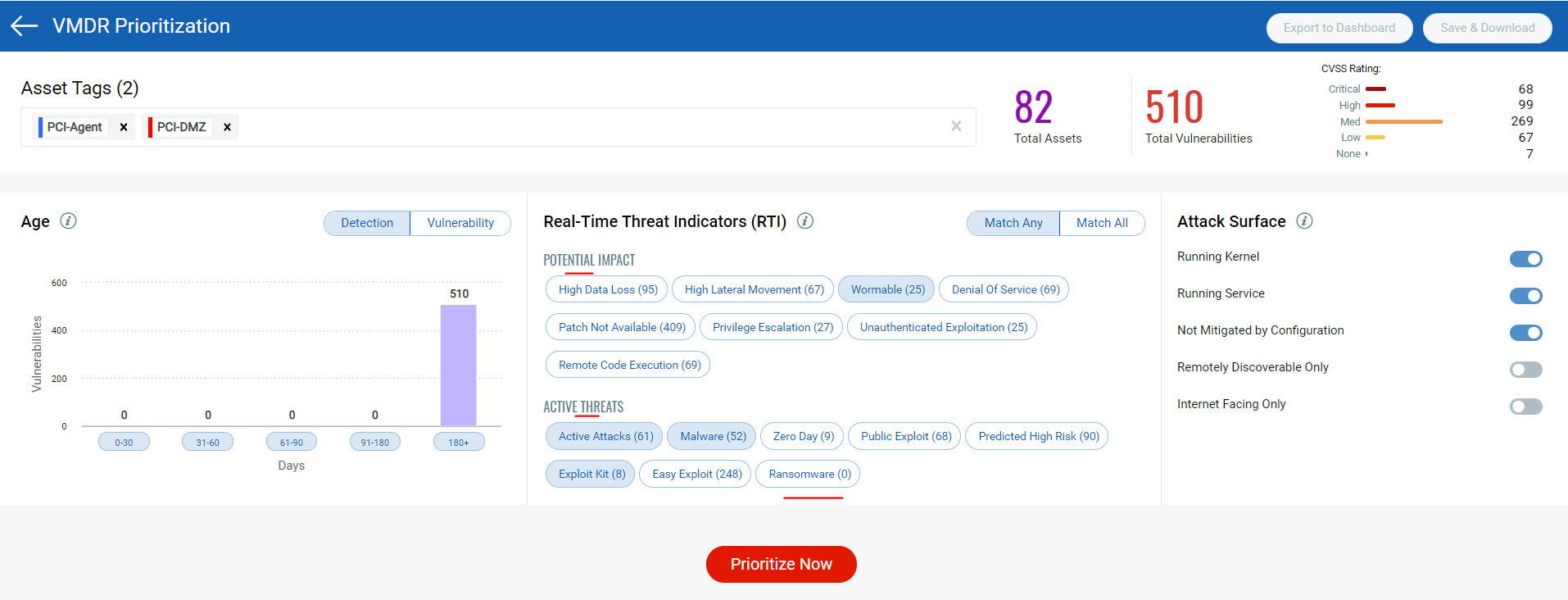
Additionally, the following query can also be used in the Vulnerabilities tab to query on active vulnerabilities associated with ransomware:
vulnerabilities.vulnerability.threatIntel.Ransomware
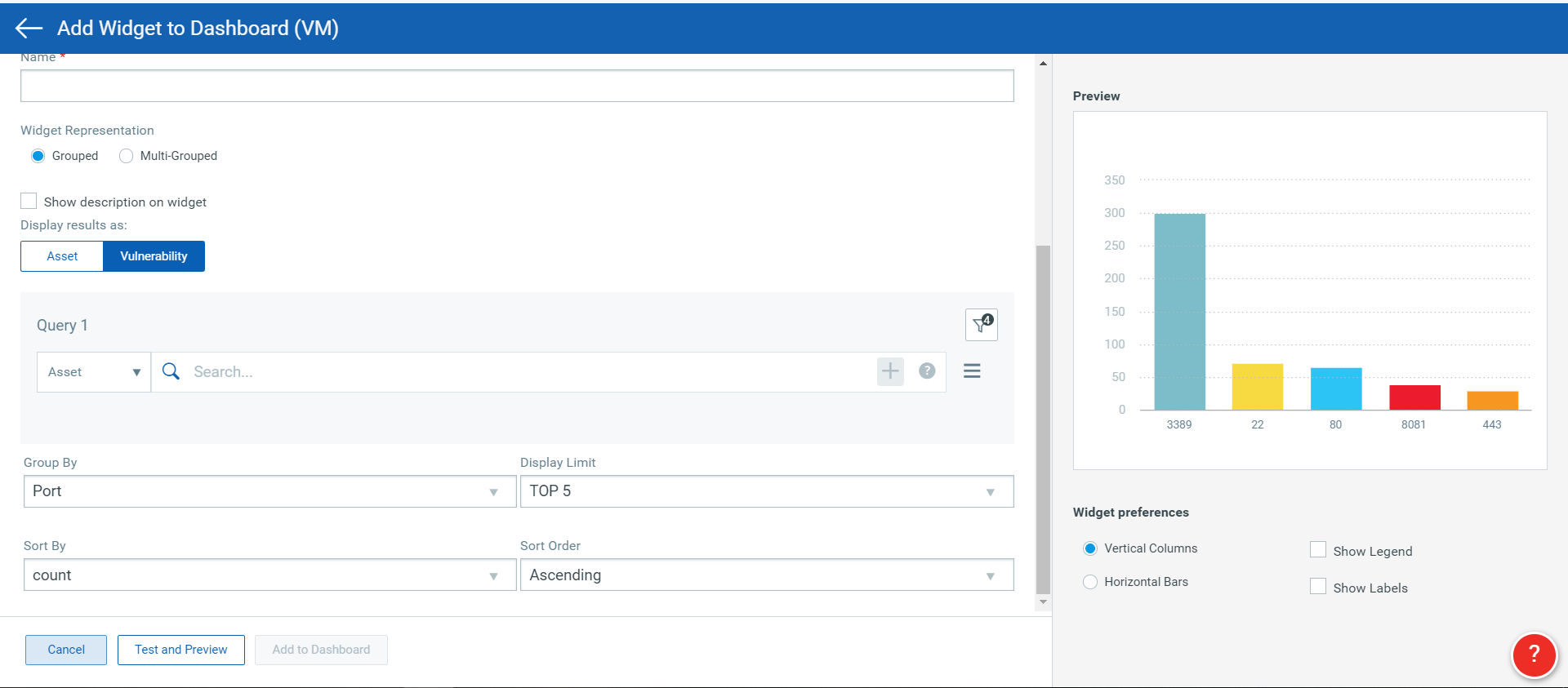
New QQL Token to Group Vulnerabilities by Port
This release adds “Group by” support to search for ports on which vulnerabilities are detected.
Qualys Policy Compliance
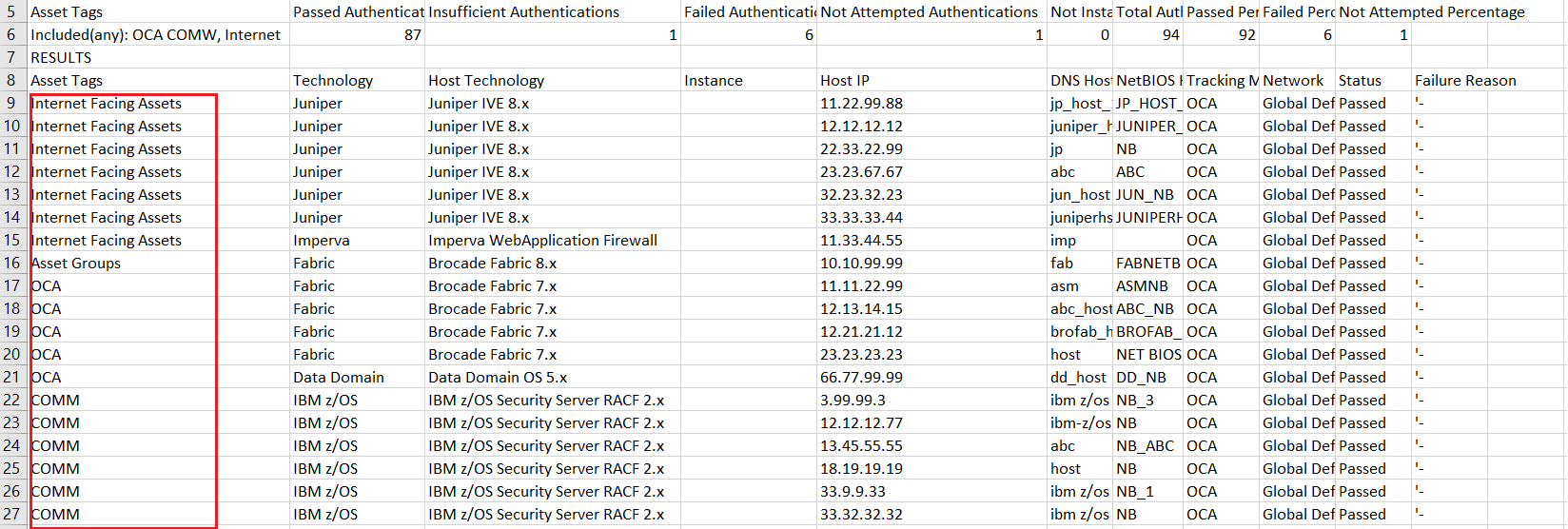
Policy Compliance Authentication Reports to Show Explicit Asset Tags
Earlier, the CSV format of authentication reports used to display the text “selected tags” text instead of displaying the names of the asset tag that are applied to the assets. with this release, the actual tag names will be displayed in the reports and users will have the option to show/hide asset tags column in authentication reports in all formats.
Increased Character Limit in the SQL Statements for UDCs
The restricted character limit in the SQL statements for user-defined controls did not allow more than 4000 characters. This limitation has been relaxed and now users can enter database UDC SQL statements with a maximum length of 32000 characters, which will enable users to use complex queries in the database UDCs.
Database UDC support for Sybase IQ
Users can now create new database user-defined controls for SAP IQ 16.x.
Qualys Cloud Agent
Additional URI parameter in Cloud Agent Installer
This release adds a mandatory parameter (WebServiceUri) to the installation command for the Windows Agent installer. This parameter will be provided in the installation instructions and will be required for new installations of Windows Agent 4.3 and higher. The agents that are already deployed will auto-update without requiring any change.
This change allows for the Windows Agent installer to be used to install an agent on any platform by providing the WebServiceUri. Previously, agent installers were specific to a platform.
Qualys Dashboards
New Templates in the Out-of-the-Box Template Library
The Templates Library will now have three additional templates, using which, users can have a single-pane-of-glass view on the dashboard for assets with specific areas of concern.
Following are the new templates that have been added:
- Qualys Severity 1 – 5 & Threat Protection – This template would help users focus on Qualys Severity Scale and the Threat Protection RTIs with severity 1 to 5 as well as “Easy exploitable & Patchable”.
- Top 10 Vulnerabilities Scorecard – This template would help users focus on top 10 vulnerabilities in various states such as New, Active, Reopened, Ignored and Fixed.
- Buffer Overflow & Kernel Vulns – With this new template, users can focus on high-risk vulnerabilities in GRand Unified Bootloader version 2.